Hello friends,
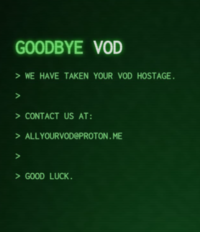
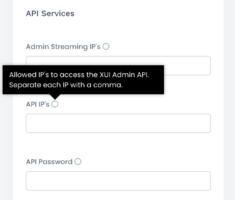
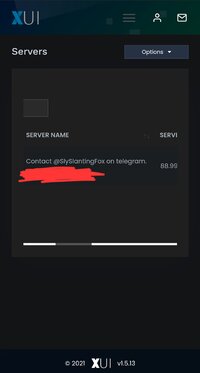
For the past week, we've been getting hacked by someone named "Slyslanting Fox." As you can see in the image, they are deleting our load balancers and renaming the main server with names like the one shown in the image. When we contacted them via Telegram, they said they would tell us how to fix the vulnerability in the panel for 500 euros. If anyone knowledgeable about this issue can help, we would greatly appreciate it.
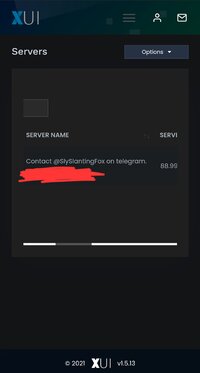
For the past week, we've been getting hacked by someone named "Slyslanting Fox." As you can see in the image, they are deleting our load balancers and renaming the main server with names like the one shown in the image. When we contacted them via Telegram, they said they would tell us how to fix the vulnerability in the panel for 500 euros. If anyone knowledgeable about this issue can help, we would greatly appreciate it.
Last edited: